Since I am going to have a three-weeks trip to China and will be working remotely, though I am not a fan of Facebook or Twitter, a VPN is still necessary for All Google Products that have been blocked since days before the sensitive June 4th.
I choose to set up my own VPN server on Linode simply because the network is relatively fast to Chinese visitors (also the $10/mo plan is pretty reasonable). I am even considering moving this blog from EC2 to Linode for its SSD storage, which might be another story.
It took me some time to set OpenVPN up last weekend. Because the server is running on Ubuntu 14.04, the official tutorial Secure Communications with OpenVPN on Ubuntu 12.04 (Precise) and Debian 7 is outdated. The most helpful resouce I found is OpenVPN on ubuntu help center. I installed and configured the server step by step following the instruction, except that I am using 2048 bit key instead the default 1024 one.
To let the VPN forward all traffic from client machines through the Linode server there is some extra work to do.
1. Edit /etc/openvpn/server.conf, uncomment push "redirect-gateway def1 bypass-dhcp" to let all IP traffic go through VPN.
2. Also change the DNS server lines to push "dhcp-option DNS 8.8.8.8" and push "dhcp-option DNS 8.8.4.4"
3. Edit /etc/sysctl.conf, change net.ipv4.ip_forward = 0 to net.ipv4.ip_forward = 1 to make IP forward allowed, then run /sbin/sysctl -p to apply the change.
4. Run /sbin/iptables -t nat -A POSTROUTING -s 10.8.0.0/24 -j SNAT --to-source a.b.c.d to properly forward the traffic through the VPN, where a.b.c.d it the public IP of the VPN server. It’s recommend to add this line to /etc/rc.local so that the change will get applied when reboot.
5. Edit client.conf, append a line redirect-gateway def1.
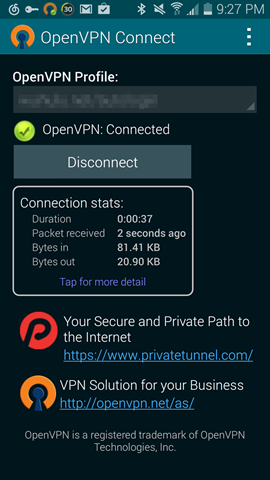
I am using Tunnelblick on Mac and OpenVPN Connect on Android phone as clients, both tested and worked well. I am feeling more confident to take this trip to my homeland now. Hope Linode will have not have got banned by that time.
自己搞VPN太容易被封了(也听说经常被封)。建议你留后备。
我只是回国用三个星期而已